
IBM Confidential Computing for Red Hat ecosystem
Confidential computing for Red Hat ecosystems

Our Price: Request a Quote
Click here to jump to more pricing!
Please Note: All Prices are Inclusive of GST
Overview:
Meet IBM Confidential Computing Container Runtime for Red Hat® Virtualization Solutions and IBM Confidential Computing Containers for Red Hat® OpenShift Container Platform® for Red Hat® OpenShift®. These two powerful products secure sensitive data from development to deployment and throughout its usage in an application. Together, they form a hardware-based confidential computing foundation to protect your workloads across hybrid environments.
Highlights
Enforced isolation for sensitive assets
Protect sensitive data, AI models and IP with infrastructure-enforced, policy-driven isolation across your hybrid environments.
Built-in AI and crypto acceleration
Run confidential workloads seamlessly with integrated AI and cryptographic acceleration in a unified stack.
Hardware-based trust and key control
Maintain full ownership and control of your encryption keys with unique hardware-based trust anchors.
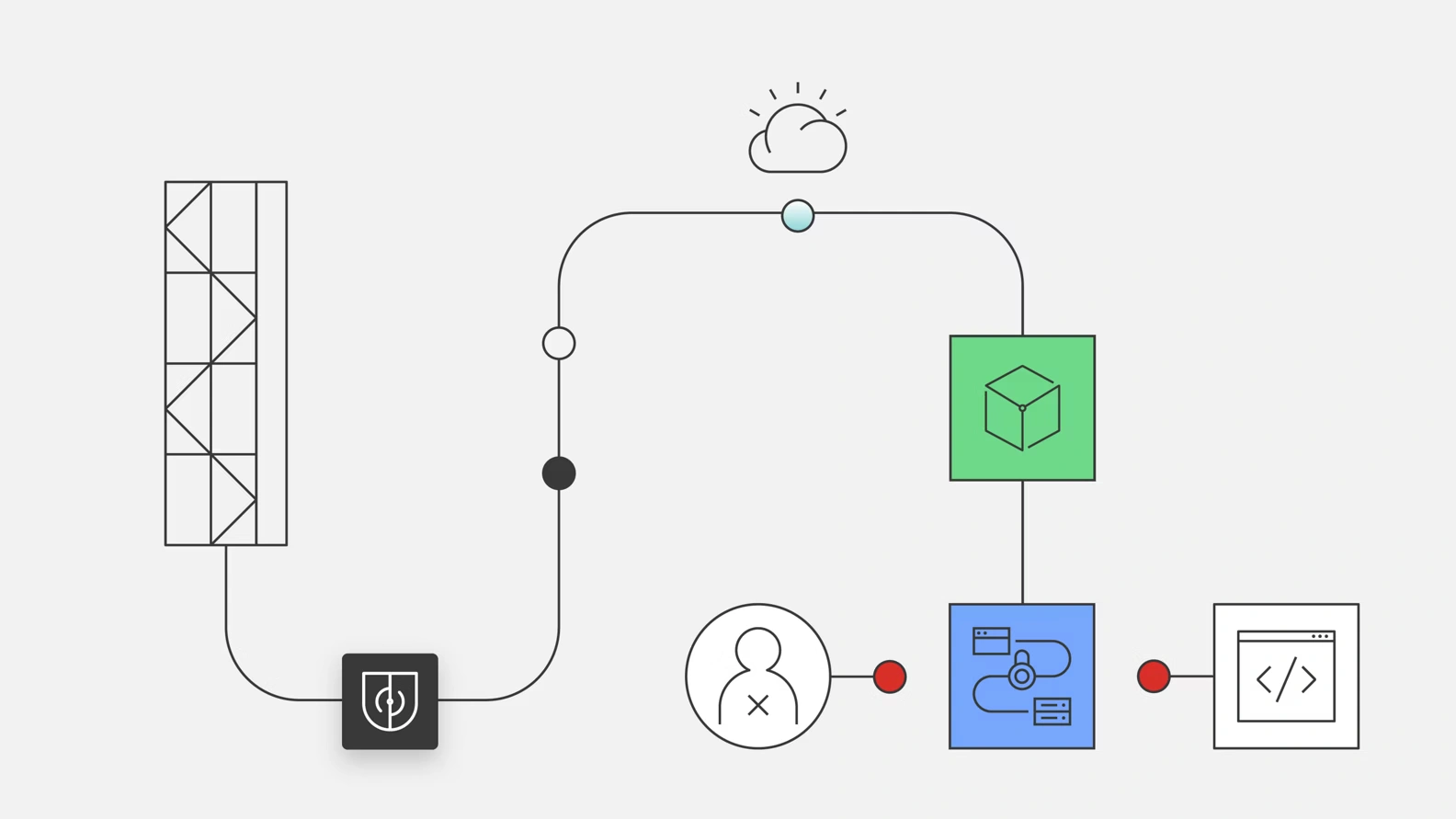
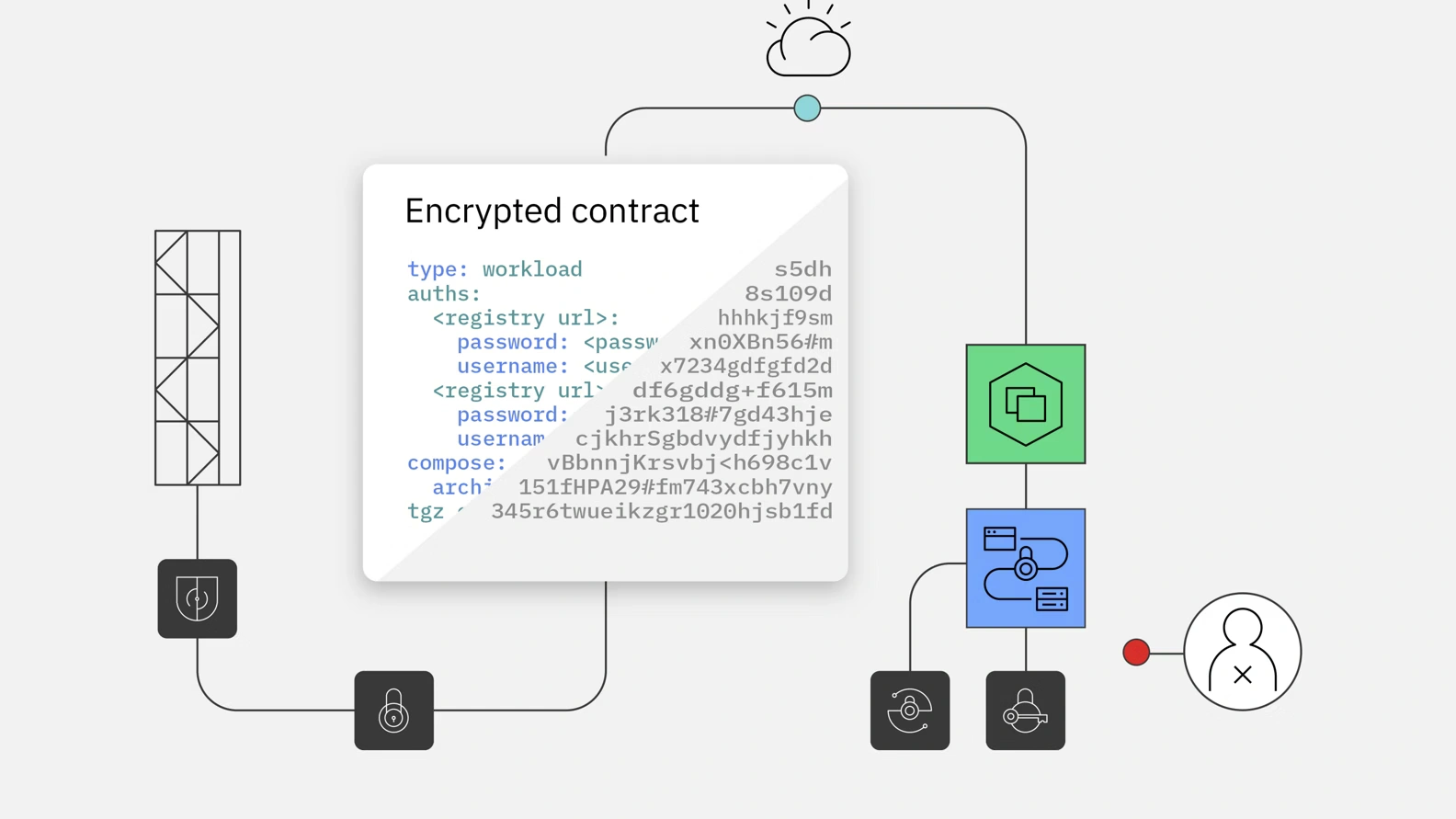
Encrypted multiparty contract
Enable verifiable workload identity at deployment by using zero-knowledge proofs and encrypted, policy-bound contracts for different personas.
Features:
Container runtime isolation
Powered by IBM Secure Execution for Linux® (SEL), IBM Confidential Computing delivers container-level isolation on Linux on Z and LinuxONE. This secures workloads from the infrastructure up during development and deployment stages.
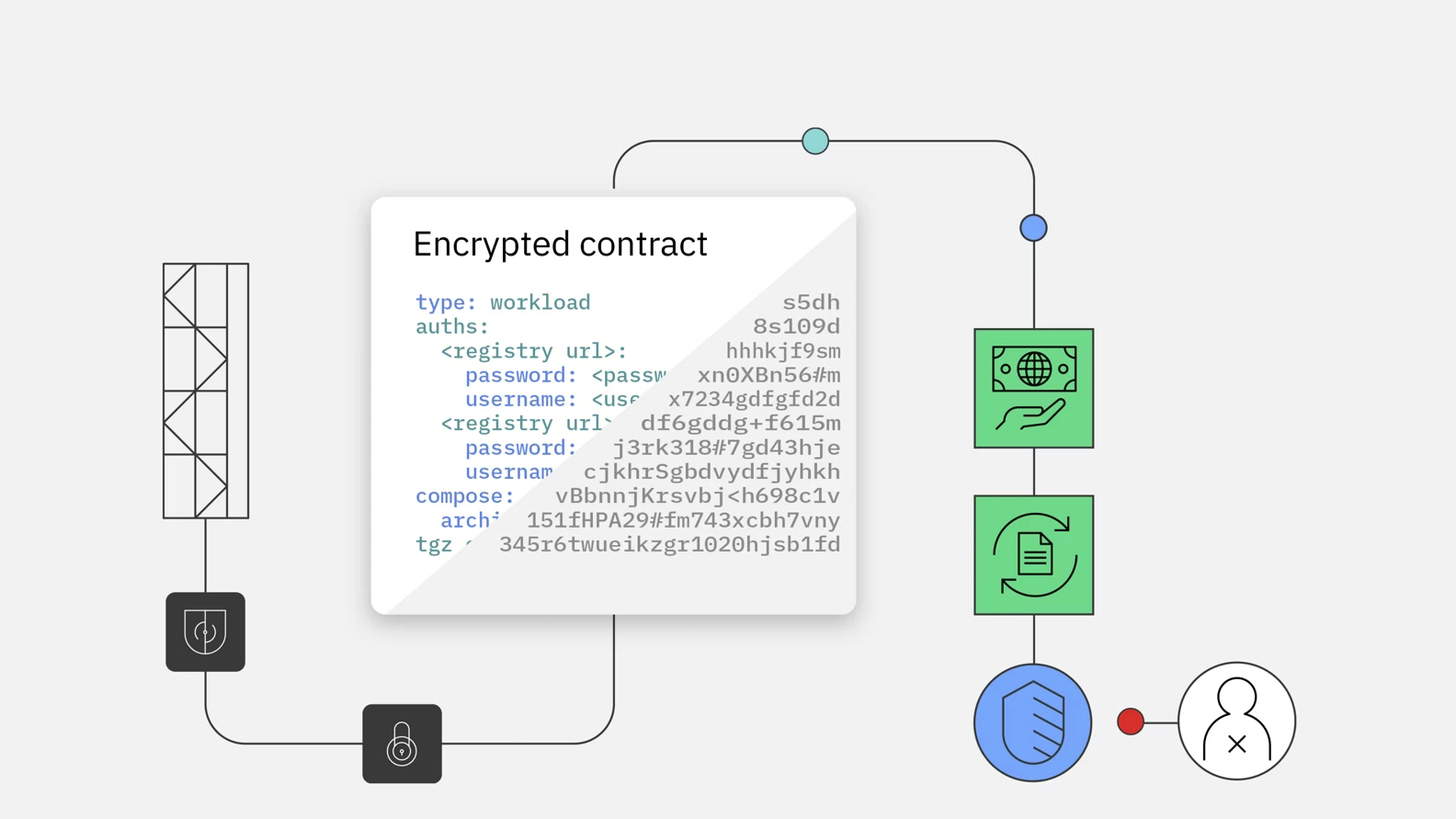
Encrypted multiparty contract enforcement
Leverage encrypted contracts to manage workload identities and enforce zero-trust policies. This feature ensures predefined roles and least-privilege access are upheld, no matter who operates the workload environment.
Embedded data-at-rest protection
With built-in cryptographic support through FIPS 140-2 Level 4 certified HSMs, both IBM Confidential Computing solutions ensure that sensitive data is always encrypted—even in shared or public cloud environments.
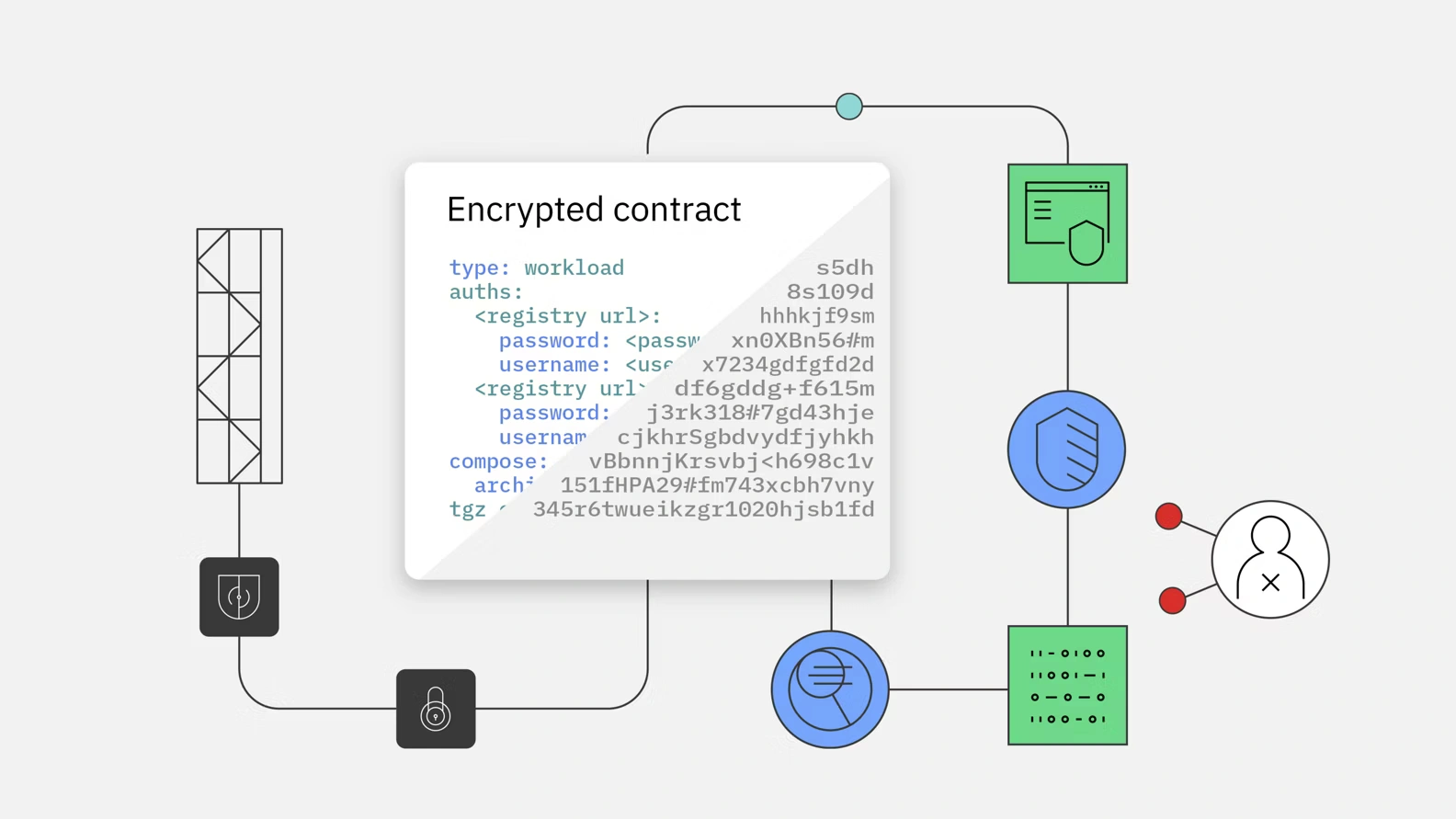
Independent attestation at deployment
IBM Confidential Computing offers secure workload verification at deployment time. Only signed, preapproved containers are allowed to run, with tamper-proof attestations and zero reliance on external trust systems.
Benefits:
Specifications:
Documentation:
Download the IBM Confidential Computing for Red Hat ecosystem (.PDF)
Pricing Notes:
- All Prices are Inclusive of GST
- Pricing and product availability subject to change without notice.
Our Price: Request a Quote
